Ompf, habe deinen Rat befolgt und die Spannung weiter angehoben. Mit 1,6V und mit 1,65V kommt es noch zum bluescreens.
Diesesmal schon relativ ohne Belastung vom Rechner. Also es sind kaum Anwendungen gelaufen... habe wieder auf 1,6v reduziert ... da tritt es später auf ... mein ich zumindest zu glauben

Sollte ich jez an den Timings wieder rumspielen? In einem deiner verlinkten Beiträge stand dirn das ich auf CL8 zurücksetzen könnte... wäre das ein nächster schritt in die richtige richtung?
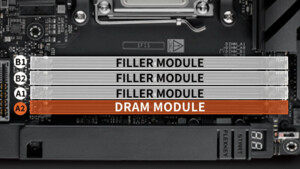
Die Probleme haben eigentlich angefangen als ich das Mainboard vollbestückt habe. Naja ich kann die zwei Riegel auch wieder raushauen... dies schränkt mich beim Videoschneiden ein wenig ein aber das wär durchaus besser wie ständige bluescreens...
Gruß Tiberius
Microsoft (R) Windows Debugger Version 6.12.0002.633 AMD64
Copyright (c) Microsoft Corporation. All rights reserved.
Loading Dump File [C:\Windows\Minidump\110810-17472-01.dmp]
Mini Kernel Dump File: Only registers and stack trace are available
Symbol search path is: paste© SRV*C:\symbols*
http://msdl.microsoft.com/download/symbols
Executable search path is:
Unable to load image \SystemRoot\system32\ntoskrnl.exe, Win32 error 0n2
*** WARNING: Unable to verify timestamp for ntoskrnl.exe
*** ERROR: Module load completed but symbols could not be loaded for ntoskrnl.exe
Windows 7 Kernel Version 7600 MP (4 procs) Free x64
Product: WinNt, suite: TerminalServer SingleUserTS Personal
Built by: 7600.16617.amd64fre.win7_gdr.100618-1621
Machine Name:
Kernel base = 0xfffff800`03051000 PsLoadedModuleList = 0xfffff800`0328ee50
Debug session time: Mon Nov 8 18:58:21.162 2010 (UTC + 1:00)
System Uptime: 0 days 0:21:00.504
Unable to load image \SystemRoot\system32\ntoskrnl.exe, Win32 error 0n2
*** WARNING: Unable to verify timestamp for ntoskrnl.exe
*** ERROR: Module load completed but symbols could not be loaded for ntoskrnl.exe
Loading Kernel Symbols
...............................................................
................................................................
.......................................
Loading User Symbols
Loading unloaded module list
.....
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck BE, {fffff880012faa80, 860000003c15121, fffff880092fa7e0, b}
Unable to load image \SystemRoot\System32\Drivers\Ntfs.sys, Win32 error 0n2
*** WARNING: Unable to verify timestamp for Ntfs.sys
*** ERROR: Module load completed but symbols could not be loaded for Ntfs.sys
***** Kernel symbols are WRONG. Please fix symbols to do analysis.
*************************************************************************
*** ***
*** ***
*** Your debugger is not using the correct symbols ***
*** ***
*** In order for this command to work properly, your symbol path ***
*** must point to .pdb files that have full type information. ***
*** ***
*** Certain .pdb files (such as the public OS symbols) do not ***
*** contain the required information. Contact the group that ***
*** provided you with these symbols if you need this command to ***
*** work. ***
*** ***
*** Type referenced: nt!_KPRCB ***
*** ***
*************************************************************************
*************************************************************************
*** ***
*** ***
*** Your debugger is not using the correct symbols ***
*** ***
*** In order for this command to work properly, your symbol path ***
*** must point to .pdb files that have full type information. ***
*** ***
*** Certain .pdb files (such as the public OS symbols) do not ***
*** contain the required information. Contact the group that ***
*** provided you with these symbols if you need this command to ***
*** work. ***
*** ***
*** Type referenced: nt!_KPRCB ***
*** ***
*************************************************************************
*************************************************************************
*** ***
*** ***
*** Your debugger is not using the correct symbols ***
*** ***
*** In order for this command to work properly, your symbol path ***
*** must point to .pdb files that have full type information. ***
*** ***
*** Certain .pdb files (such as the public OS symbols) do not ***
*** contain the required information. Contact the group that ***
*** provided you with these symbols if you need this command to ***
*** work. ***
*** ***
*** Type referenced: nt!_KPRCB ***
*** ***
*************************************************************************
Probably caused by : ntoskrnl.exe ( nt+70740 )
Followup: MachineOwner
---------
3: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
ATTEMPTED_WRITE_TO_READONLY_MEMORY (be)
An attempt was made to write to readonly memory. The guilty driver is on the
stack trace (and is typically the current instruction pointer).
When possible, the guilty driver's name (Unicode string) is printed on
the bugcheck screen and saved in KiBugCheckDriver.
Arguments:
Arg1: fffff880012faa80, Virtual address for the attempted write.
Arg2: 0860000003c15121, PTE contents.
Arg3: fffff880092fa7e0, (reserved)
Arg4: 000000000000000b, (reserved)
Debugging Details:
------------------
***** Kernel symbols are WRONG. Please fix symbols to do analysis.
*************************************************************************
*** ***
*** ***
*** Your debugger is not using the correct symbols ***
*** ***
*** In order for this command to work properly, your symbol path ***
*** must point to .pdb files that have full type information. ***
*** ***
*** Certain .pdb files (such as the public OS symbols) do not ***
*** contain the required information. Contact the group that ***
*** provided you with these symbols if you need this command to ***
*** work. ***
*** ***
*** Type referenced: nt!_KPRCB ***
*** ***
*************************************************************************
*************************************************************************
*** ***
*** ***
*** Your debugger is not using the correct symbols ***
*** ***
*** In order for this command to work properly, your symbol path ***
*** must point to .pdb files that have full type information. ***
*** ***
*** Certain .pdb files (such as the public OS symbols) do not ***
*** contain the required information. Contact the group that ***
*** provided you with these symbols if you need this command to ***
*** work. ***
*** ***
*** Type referenced: nt!_KPRCB ***
*** ***
*************************************************************************
*************************************************************************
*** ***
*** ***
*** Your debugger is not using the correct symbols ***
*** ***
*** In order for this command to work properly, your symbol path ***
*** must point to .pdb files that have full type information. ***
*** ***
*** Certain .pdb files (such as the public OS symbols) do not ***
*** contain the required information. Contact the group that ***
*** provided you with these symbols if you need this command to ***
*** work. ***
*** ***
*** Type referenced: nt!_KPRCB ***
*** ***
*************************************************************************
ADDITIONAL_DEBUG_TEXT:
Use '!findthebuild' command to search for the target build information.
If the build information is available, run '!findthebuild -s ; .reload' to set symbol path and load symbols.
MODULE_NAME: nt
FAULTING_MODULE: fffff80003051000 nt
DEBUG_FLR_IMAGE_TIMESTAMP: 4c1c44a9
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: VISTA_DRIVER_FAULT
BUGCHECK_STR: 0xBE
CURRENT_IRQL: 0
LAST_CONTROL_TRANSFER: from fffff80003141ae2 to fffff800030c1740
STACK_TEXT:
fffff880`092fa678 fffff800`03141ae2 : 00000000`000000be fffff880`012faa80 08600000`03c15121 fffff880`092fa7e0 : nt+0x70740
fffff880`092fa680 00000000`000000be : fffff880`012faa80 08600000`03c15121 fffff880`092fa7e0 00000000`0000000b : nt+0xf0ae2
fffff880`092fa688 fffff880`012faa80 : 08600000`03c15121 fffff880`092fa7e0 00000000`0000000b fffffa80`06d0ea10 : 0xbe
fffff880`092fa690 08600000`03c15121 : fffff880`092fa7e0 00000000`0000000b fffffa80`06d0ea10 00000000`00000000 : Ntfs+0xb8a80
fffff880`092fa698 fffff880`092fa7e0 : 00000000`0000000b fffffa80`06d0ea10 00000000`00000000 00000000`00000000 : 0x8600000`03c15121
fffff880`092fa6a0 00000000`0000000b : fffffa80`06d0ea10 00000000`00000000 00000000`00000000 fffff800`0324de00 : 0xfffff880`092fa7e0
fffff880`092fa6a8 fffffa80`06d0ea10 : 00000000`00000000 00000000`00000000 fffff800`0324de00 fffff880`092fa800 : 0xb
fffff880`092fa6b0 00000000`00000000 : 00000000`00000000 fffff800`0324de00 fffff880`092fa800 00000000`00000000 : 0xfffffa80`06d0ea10
STACK_COMMAND: kb
FOLLOWUP_IP:
nt+70740
fffff800`030c1740 48894c2408 mov qword ptr [rsp+8],rcx
SYMBOL_STACK_INDEX: 0
SYMBOL_NAME: nt+70740
FOLLOWUP_NAME: MachineOwner
IMAGE_NAME: ntoskrnl.exe
BUCKET_ID: WRONG_SYMBOLS
Followup: MachineOwner
---------
3: kd> lmvm nt
start end module name
fffff800`03051000 fffff800`0362d000 nt T (no symbols)
Loaded symbol image file: ntoskrnl.exe
Image path: \SystemRoot\system32\ntoskrnl.exe
Image name: ntoskrnl.exe
Timestamp: Sat Jun 19 06:16:41 2010 (4C1C44A9)
CheckSum: 005489D7
ImageSize: 005DC000
Translations: 0000.04b0 0000.04e4 0409.04b0 0409.04e4