Hallo,
ich klinke mich mal hier ein, denn ich habe auch probleme mit mehreren "STOP:" fehlern.
Ich habe alle fehler mit dem debugg-tool ausgelesen und habe folgendes heraus bekommen
Mein Betriebssystem ist Windows 7 Home Premium 64bit:
Als erster Stop fehler kamm diese Meldung 0x0000001E = amdppm.sys wurde angezeigt, da war Windows 7 ca.2 stunden im Betrieb habe gesurft.
Nach einem Neustart kam diese meldung 0x0000001E = ntkrnlmp.exe
Nagut mache ich halt wieder einen Neustart und das system lief ca. 2 stu stabil bis dann dieses angezeigt wurde 0x000000D1 = CLASSPNP.sys
Ich bin aber auch nicht schlauer daraus geworden.
Was sind das für fehler und wie kann ich die beheben, und kommt mir jetzt nicht damit
das ich alles wieder neuinstallieren muß

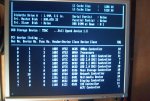
Hier auswertung
ntkrnlmp.exe
Microsoft (R) Windows Debugger Version 6.11.0001.404 AMD64
Copyright (c) Microsoft Corporation. All rights reserved.
Loading Dump File [C:\Windows\Minidump\082610-25662-01.dmp]
Mini Kernel Dump File: Only registers and stack trace are available
WARNING: Whitespace at start of path element
WARNING: Whitespace at start of path element
Symbol search path is: SRV*C:\symbols*
http://msdl.microsoft.com/download/symbols
Executable search path is: c:\windows\System32; c:\windows\system\System32
Windows 7 Kernel Version 7600 MP (4 procs) Free x64
Product: WinNt, suite: TerminalServer SingleUserTS Personal
Built by: 7600.16617.amd64fre.win7_gdr.100618-1621
Machine Name:
Kernel base = 0xfffff800`0284c000 PsLoadedModuleList = 0xfffff800`02a89e50
Debug session time: Thu Aug 26 12:19:59.031 2010 (GMT+2)
System Uptime: 0 days 1:41:27.982
Loading Kernel Symbols
...............................................................
................................................................
............................
Loading User Symbols
Loading unloaded module list
........
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck 1E, {0, 0, 0, 0}
Probably caused by : ntkrnlmp.exe ( nt!KiKernelCalloutExceptionHandler+e )
Followup: MachineOwner
---------
2: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
KMODE_EXCEPTION_NOT_HANDLED (1e)
This is a very common bugcheck. Usually the exception address pinpoints
the driver/function that caused the problem. Always note this address
as well as the link date of the driver/image that contains this address.
Arguments:
Arg1: 0000000000000000, The exception code that was not handled
Arg2: 0000000000000000, The address that the exception occurred at
Arg3: 0000000000000000, Parameter 0 of the exception
Arg4: 0000000000000000, Parameter 1 of the exception
Debugging Details:
------------------
EXCEPTION_CODE: (Win32) 0 (0) - Der Vorgang wurde erfolgreich beendet.
FAULTING_IP:
+0
00000000`00000000 ?? ???
EXCEPTION_PARAMETER1: 0000000000000000
EXCEPTION_PARAMETER2: 0000000000000000
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: VISTA_DRIVER_FAULT
BUGCHECK_STR: 0x1E
PROCESS_NAME: System
CURRENT_IRQL: 2
EXCEPTION_RECORD: fffff88002f8b328 -- (.exr 0xfffff88002f8b328)
ExceptionAddress: fffff800028c613b (nt!KiTimerWaitTest+0x000000000000001b)
ExceptionCode: c0000005 (Access violation)
ExceptionFlags: 00000000
NumberParameters: 2
Parameter[0]: 0000000000000000
Parameter[1]: ffffffffffffffff
Attempt to read from address ffffffffffffffff
TRAP_FRAME: fffff88002f8b3d0 -- (.trap 0xfffff88002f8b3d0)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=da55e69405611a97 rbx=0000000000000000 rcx=fffff88002f63180
rdx=fffffa8004b5e230 rsi=0000000000000000 rdi=0000000000000000
rip=fffff800028c613b rsp=fffff88002f8b560 rbp=000000000005f46c
r8=fffff88002f65301 r9=0000000000000002 r10=000000000000006c
r11=0000000000000000 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl nz na pe nc
nt!KiTimerWaitTest+0x1b:
fffff800`028c613b 8bc8 mov ecx,eax
Resetting default scope
LAST_CONTROL_TRANSFER: from fffff800028b446e to fffff800028bc710
STACK_TEXT:
fffff880`02f8a418 fffff800`028b446e : fffff880`02f8a778 00000000`00000011 fffff880`02f8ab90 fffff800`028e9668 : nt!KeBugCheck
fffff880`02f8a420 fffff800`028e240d : fffff800`02acab7c fffff800`02a04e84 fffff800`0284c000 fffff880`02f8b328 : nt!KiKernelCalloutExceptionHandler+0xe
fffff880`02f8a450 fffff800`028e9a90 : fffff800`02a0bb14 fffff880`02f8a4c8 fffff880`02f8b328 fffff800`0284c000 : nt!RtlpExecuteHandlerForException+0xd
fffff880`02f8a480 fffff800`028f69ef : fffff880`02f8b328 fffff880`02f8ab90 fffff880`00000000 fffff880`02f8b608 : nt!RtlDispatchException+0x410
fffff880`02f8ab60 fffff800`028bbd82 : fffff880`02f8b328 fffffa80`04b5e230 fffff880`02f8b3d0 71f4a3f4`bef73d15 : nt!KiDispatchException+0x16f
fffff880`02f8b1f0 fffff800`028ba68a : 00000000`00002080 fffff880`1005f66e fffffa80`05d63000 fffffa80`05d63000 : nt!KiExceptionDispatch+0xc2
fffff880`02f8b3d0 fffff800`028c613b : fffff800`02a36e80 fffffa80`04436b60 fffffa80`073a7300 fffff880`0fe0c095 : nt!KiGeneralProtectionFault+0x10a
fffff880`02f8b560 fffff800`028c7d7d : fffffa80`05021c20 fffffa80`05021c68 fffffa80`05021c68 00000000`00000000 : nt!KiTimerWaitTest+0x1b
fffff880`02f8b5e0 fffff800`028c84be : 0000000e`2cb86098 fffff880`02f8bc58 00000000`0005f46c fffff880`02f66308 : nt!KiProcessExpiredTimerList+0x6d
fffff880`02f8bc30 fffff800`028c7cb7 : 00000003`79fe23c1 00000003`0005f46c 00000003`79fe2312 00000000`0000006c : nt!KiTimerExpiration+0x1be
fffff880`02f8bcd0 fffff800`028c4eea : fffff880`02f63180 fffff880`02f6dfc0 00000000`00000000 fffff880`0fe85bdc : nt!KiRetireDpcList+0x277
fffff880`02f8bd80 00000000`00000000 : fffff880`02f8c000 fffff880`02f86000 fffff880`02f8bd40 00000000`00000000 : nt!KiIdleLoop+0x5a
STACK_COMMAND: kb
FOLLOWUP_IP:
nt!KiKernelCalloutExceptionHandler+e
fffff800`028b446e 90 nop
SYMBOL_STACK_INDEX: 1
SYMBOL_NAME: nt!KiKernelCalloutExceptionHandler+e
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
DEBUG_FLR_IMAGE_TIMESTAMP: 4c1c44a9
FAILURE_BUCKET_ID: X64_0x1E_nt!KiKernelCalloutExceptionHandler+e
BUCKET_ID: X64_0x1E_nt!KiKernelCalloutExceptionHandler+e
Followup: MachineOwner
-----------------------------------------------------------------------------------------------------------------------------
Hier auswertung
amdppm.sys
Microsoft (R) Windows Debugger Version 6.11.0001.404 AMD64
Copyright (c) Microsoft Corporation. All rights reserved.
Loading Dump File [C:\Windows\Minidump\082610-17113-01.dmp]
Mini Kernel Dump File: Only registers and stack trace are available
WARNING: Whitespace at start of path element
Symbol search path is: SRV*C:\symbols*
http://msdl.microsoft.com/download/symbols
Executable search path is: c:\windows\System32; c:\windows\system\System32
Windows 7 Kernel Version 7600 MP (4 procs) Free x64
Product: WinNt, suite: TerminalServer SingleUserTS Personal
Built by: 7600.16617.amd64fre.win7_gdr.100618-1621
Machine Name:
Kernel base = 0xfffff800`02860000 PsLoadedModuleList = 0xfffff800`02a9de50
Debug session time: Thu Aug 26 18:04:12.317 2010 (GMT+2)
System Uptime: 0 days 1:19:31.894
Loading Kernel Symbols
...............................................................
................................................................
..............................
Loading User Symbols
Loading unloaded module list
.....
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck 1E, {0, 0, 0, 0}
Probably caused by : amdppm.sys ( amdppm!C1Halt+2 )
Followup: MachineOwner
---------
2: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
KMODE_EXCEPTION_NOT_HANDLED (1e)
This is a very common bugcheck. Usually the exception address pinpoints
the driver/function that caused the problem. Always note this address
as well as the link date of the driver/image that contains this address.
Arguments:
Arg1: 0000000000000000, The exception code that was not handled
Arg2: 0000000000000000, The address that the exception occurred at
Arg3: 0000000000000000, Parameter 0 of the exception
Arg4: 0000000000000000, Parameter 1 of the exception
Debugging Details:
------------------
EXCEPTION_CODE: (Win32) 0 (0) - Der Vorgang wurde erfolgreich beendet.
FAULTING_IP:
+0
00000000`00000000 ?? ???
EXCEPTION_PARAMETER1: 0000000000000000
EXCEPTION_PARAMETER2: 0000000000000000
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: VISTA_DRIVER_FAULT
BUGCHECK_STR: 0x1E
PROCESS_NAME: System
CURRENT_IRQL: d
EXCEPTION_RECORD: fffff88002f8b808 -- (.exr 0xfffff88002f8b808)
ExceptionAddress: fffff800028d7391 (nt!KeAccumulateTicks+0x0000000000000141)
ExceptionCode: c000001d (Illegal instruction)
ExceptionFlags: 00000000
NumberParameters: 0
TRAP_FRAME: fffff88002f8b8b0 -- (.trap 0xfffff88002f8b8b0)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=acaeb078b3307620 rbx=0000000000000000 rcx=0000000000000011
rdx=00000000000162d3 rsi=0000000000000000 rdi=0000000000000000
rip=fffff800028d7391 rsp=fffff88002f8ba40 rbp=0000000000000000
r8=000000000001a650 r9=0000000000000000 r10=0000000000007851
r11=fffffa800716e318 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl zr na po nc
nt!KeAccumulateTicks+0x141:
fffff800`028d7391 408ac5 mov al,bpl
Resetting default scope
LAST_CONTROL_TRANSFER: from fffff800028c846e to fffff800028d0710
STACK_TEXT:
fffff880`02f8a8f8 fffff800`028c846e : 00000000`00000000 fffff800`02a755f8 fffff880`02f8b070 fffff800`028fd668 : nt!KeBugCheck
fffff880`02f8a900 fffff800`028f640d : fffff800`02adeedc fffff800`02a17dac fffff800`02860000 fffff880`02f8b808 : nt!KiKernelCalloutExceptionHandler+0xe
fffff880`02f8a930 fffff800`028fda90 : fffff800`02a1fb14 fffff880`02f8a9a8 fffff880`02f8b808 fffff800`02860000 : nt!RtlpExecuteHandlerForException+0xd
fffff880`02f8a960 fffff800`0290a9ef : fffff880`02f8b808 fffff880`02f8b070 fffff880`00000000 00000000`00000000 : nt!RtlDispatchException+0x410
fffff880`02f8b040 fffff800`028cfd82 : fffff880`02f8b808 fffff880`02f63180 fffff880`02f8b8b0 00000000`00002710 : nt!KiDispatchException+0x16f
fffff880`02f8b6d0 fffff800`028cdedf : fffff880`02f8b8b0 fffff880`1002e60d fffffa80`05ad7000 fffffa80`00000000 : nt!KiExceptionDispatch+0xc2
fffff880`02f8b8b0 fffff800`028d7391 : 00000000`00000000 fffff880`0ffdc6a3 00000000`00000001 00000000`00000001 : nt!KiInvalidOpcodeFault+0x11f
fffff880`02f8ba40 fffff800`028dd618 : fffffa80`05ad7000 fffff880`0ffc571c 00000000`00002710 fffffa80`05299500 : nt!KeAccumulateTicks+0x141
fffff880`02f8bad0 fffff800`028dd3a1 : 00000000`00000000 fffff880`02f8bb80 fffff880`02f63180 00000000`00000001 : nt!KeUpdateRunTime+0xb8
fffff880`02f8bb00 fffff880`03f1e7f2 : fffff800`028de24a 00000000`00256c4e fffffa80`05299598 fffff880`02f6dfc0 : nt!KiSecondaryClockInterrupt+0x131
fffff880`02f8bc98 fffff800`028de24a : 00000000`00256c4e fffffa80`05299598 fffff880`02f6dfc0 00000000`00000001 : amdppm!C1Halt+0x2
fffff880`02f8bca0 fffff800`028d8ebc : fffff880`02f63180 fffff880`00000000 00000000`00000000 fffff880`0fe54bdc : nt!PoIdle+0x53a
fffff880`02f8bd80 00000000`00000000 : fffff880`02f8c000 fffff880`02f86000 fffff880`02f8bd40 00000000`00000000 : nt!KiIdleLoop+0x2c
STACK_COMMAND: kb
FOLLOWUP_IP:
amdppm!C1Halt+2
fffff880`03f1e7f2 c3 ret
SYMBOL_STACK_INDEX: a
SYMBOL_NAME: amdppm!C1Halt+2
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: amdppm
IMAGE_NAME: amdppm.sys
DEBUG_FLR_IMAGE_TIMESTAMP: 4a5bc0fd
FAILURE_BUCKET_ID: X64_0x1E_amdppm!C1Halt+2
BUCKET_ID: X64_0x1E_amdppm!C1Halt+2
Followup: MachineOwner
-----------------------------------------------------------------------------------------------------------------------------
Hier auswertung
CLASSPNP.SYS
Microsoft (R) Windows Debugger Version 6.11.0001.404 AMD64
Copyright (c) Microsoft Corporation. All rights reserved.
Loading Dump File [C:\Windows\Minidump\082610-17924-01.dmp]
Mini Kernel Dump File: Only registers and stack trace are available
WARNING: Whitespace at start of path element
WARNING: Whitespace at start of path element
Symbol search path is: SRV*C:\symbols*
http://msdl.microsoft.com/download/symbols
Executable search path is: c:\windows\System32; c:\windows\system\System32;
http://www.alexander.com/SymServe
Windows 7 Kernel Version 7600 MP (4 procs) Free x64
Product: WinNt, suite: TerminalServer SingleUserTS Personal
Built by: 7600.16617.amd64fre.win7_gdr.100618-1621
Machine Name:
Kernel base = 0xfffff800`02810000 PsLoadedModuleList = 0xfffff800`02a4de50
Debug session time: Thu Aug 26 18:06:57.235 2010 (GMT+2)
System Uptime: 0 days 0:01:38.186
Loading Kernel Symbols
...............................................................
................................................................
............................
Loading User Symbols
Loading unloaded module list
....
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck D1, {fffff8005f9d0007, e, 8, fffff8005f9d0007}
Probably caused by : CLASSPNP.SYS ( CLASSPNP!TransferPktComplete+227 )
Followup: MachineOwner
---------
2: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
DRIVER_IRQL_NOT_LESS_OR_EQUAL (d1)
An attempt was made to access a pageable (or completely invalid) address at an
interrupt request level (IRQL) that is too high. This is usually
caused by drivers using improper addresses.
If kernel debugger is available get stack backtrace.
Arguments:
Arg1: fffff8005f9d0007, memory referenced
Arg2: 000000000000000e, IRQL
Arg3: 0000000000000008, value 0 = read operation, 1 = write operation
Arg4: fffff8005f9d0007, address which referenced memory
Debugging Details:
------------------
READ_ADDRESS: GetPointerFromAddress: unable to read from fffff80002ab80e0
fffff8005f9d0007
CURRENT_IRQL: e
FAULTING_IP:
+0
fffff800`5f9d0007 ?? ???
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: VISTA_DRIVER_FAULT
BUGCHECK_STR: 0xD1
PROCESS_NAME: System
TRAP_FRAME: fffff88002f8b890 -- (.trap 0xfffff88002f8b890)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=fffff8005f9d0007 rbx=0000000000000000 rcx=fffff88002f63180
rdx=0000003900000000 rsi=0000000000000000 rdi=0000000000000000
rip=fffff8005f9d0007 rsp=fffff88002f8ba20 rbp=fffff880009e7180
r8=fffff88002f6dfc0 r9=000000000b855499 r10=fffff88002f67e40
r11=fffffa8004e219f4 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei ng nz na pe nc
fffff800`5f9d0007 ?? ???
Resetting default scope
LAST_CONTROL_TRANSFER: from fffff8000287fca9 to fffff80002880740
FAILED_INSTRUCTION_ADDRESS:
+0
fffff800`5f9d0007 ?? ???
STACK_TEXT:
fffff880`02f8b748 fffff800`0287fca9 : 00000000`0000000a fffff800`5f9d0007 00000000`0000000e 00000000`00000008 : nt!KeBugCheckEx
fffff880`02f8b750 fffff800`0287e920 : 00000000`00000000 00000000`00000003 00000000`00000001 00000000`00000000 : nt!KiBugCheckDispatch+0x69
fffff880`02f8b890 fffff800`5f9d0007 : fffff880`018d9110 00000000`ffffffff fffffa80`04ade060 fffffa80`03e25e60 : nt!KiPageFault+0x260
fffff880`02f8ba20 fffff880`018d9110 : 00000000`ffffffff fffffa80`04ade060 fffffa80`03e25e60 fffff8a0`03784000 : 0xfffff800`5f9d0007
fffff880`02f8ba28 00000000`ffffffff : fffffa80`04ade060 fffffa80`03e25e60 fffff8a0`03784000 fffff880`018bf947 : CLASSPNP!WPP_GLOBAL_Control
fffff880`02f8ba30 fffffa80`04ade060 : fffffa80`03e25e60 fffff8a0`03784000 fffff880`018bf947 fffffa80`060ce010 : 0xffffffff
fffff880`02f8ba38 fffffa80`03e25e60 : fffff8a0`03784000 fffff880`018bf947 fffffa80`060ce010 00000000`00000003 : 0xfffffa80`04ade060
fffff880`02f8ba40 fffff8a0`03784000 : fffff880`018bf947 fffffa80`060ce010 00000000`00000003 00000000`ffffffff : 0xfffffa80`03e25e60
fffff880`02f8ba48 fffff880`018bf947 : fffffa80`060ce010 00000000`00000003 00000000`ffffffff 00000000`00000000 : 0xfffff8a0`03784000
fffff880`02f8ba50 fffff800`0288d618 : 00000000`00000000 fffffa80`04797960 fffffa80`05583400 fffffa80`05581b00 : CLASSPNP!TransferPktComplete+0x227
fffff880`02f8bad0 fffff800`0288cb1a : 00000000`00000000 fffff880`02f8bb80 00000000`00000001 fffffa80`05583490 : nt!KeUpdateRunTime+0xb8
fffff880`02f8bb00 fffff880`03e5c7f2 : fffff800`0288e24a 00000000`00256c4e fffffa80`05581bb8 fffff880`02f6dfc0 : nt!KiIpiInterrupt+0x12a
fffff880`02f8bc98 fffff800`0288e24a : 00000000`00256c4e fffffa80`05581bb8 fffff880`02f6dfc0 00000000`00000002 : amdppm!C1Halt+0x2
fffff880`02f8bca0 fffff800`02888ebc : fffff880`02f63180 fffff880`00000000 00000000`00000000 fffff880`01002880 : nt!PoIdle+0x53a
fffff880`02f8bd80 00000000`00000000 : fffff880`02f8c000 fffff880`02f86000 fffff880`02f8bd40 00000000`00000000 : nt!KiIdleLoop+0x2c
STACK_COMMAND: kb
FOLLOWUP_IP:
CLASSPNP!TransferPktComplete+227
fffff880`018bf947 488d9e30010000 lea rbx,[rsi+130h]
SYMBOL_STACK_INDEX: 9
SYMBOL_NAME: CLASSPNP!TransferPktComplete+227
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: CLASSPNP
IMAGE_NAME: CLASSPNP.SYS
DEBUG_FLR_IMAGE_TIMESTAMP: 4a5bc11e
FAILURE_BUCKET_ID: X64_0xD1_CODE_AV_BAD_IP_CLASSPNP!TransferPktComplete+227
BUCKET_ID: X64_0xD1_CODE_AV_BAD_IP_CLASSPNP!TransferPktComplete+227
Followup: MachineOwner
---------